• Remote substation & DER protection (AMI/MDMS, EMS/DMS)
• Secure vendor/contractor access without VPN exposure
• Legacy PLC/IED shielding and site-to-site overlay
• Faster performance vs. traditional VPN alternatives
• Free Trial: make one host invisible in minutes
- admin@topsccc.tech
- Mohan Nagar, Baner, Pune
Energy & Renewables Network
ENERGY & RENEWABLES — ZERO-TRUST OT PROTECTION
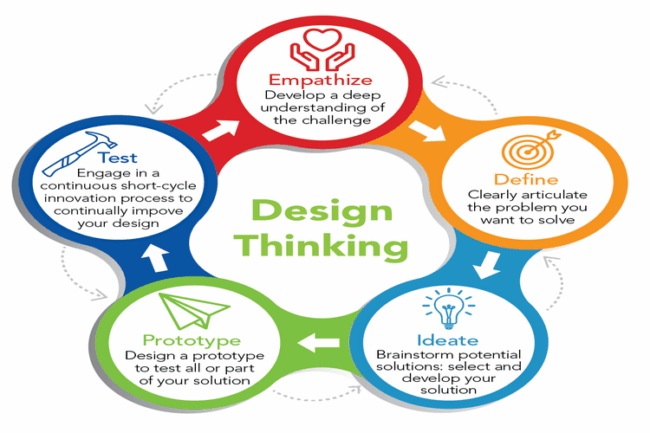
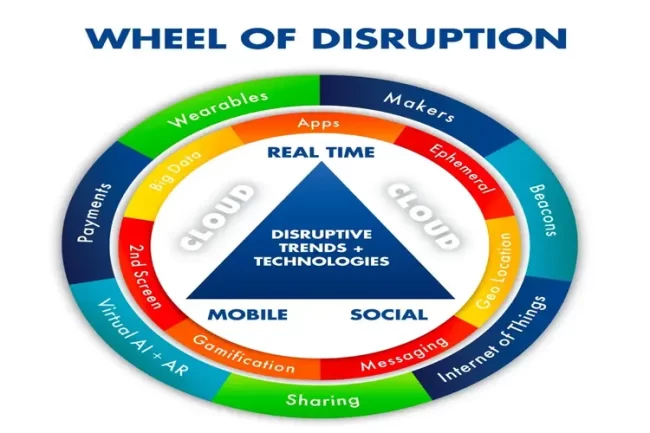
Calculate your secure remote access and network cloaking needs for power plants, wind/solar farms, and remote substations. Block reconnaissance, eliminate credential theft with passwordless MFA, and microsegment critical assets.
Make wind turbines, PV inverters, relays & gateways undiscoverable to external scans—what attackers can’t see, they can’t target.
Eliminate stolen credentials/MFA fatigue. Biometric or FIDO2 access to OT networks and apps—no passwords to phish.
Apply least-privilege, per-asset access down to DCS/SCADA endpoints to stop lateral movement across plants and farms.
Shield unpatchable controllers and IEDs with a strong overlay that reduces exposure without rewiring your network.
Enable safe vendor and field-engineer access to remote substations and renewable sites—without opening inbound ports.
Segment AMI/MDMS, EMS/DMS, and battery management systems to prevent manipulation and contain incidents.
Block AI-powered recon and credential attacks at the source to reduce risk with superior Return on Mitigation.
Energy & Renewables OT Services
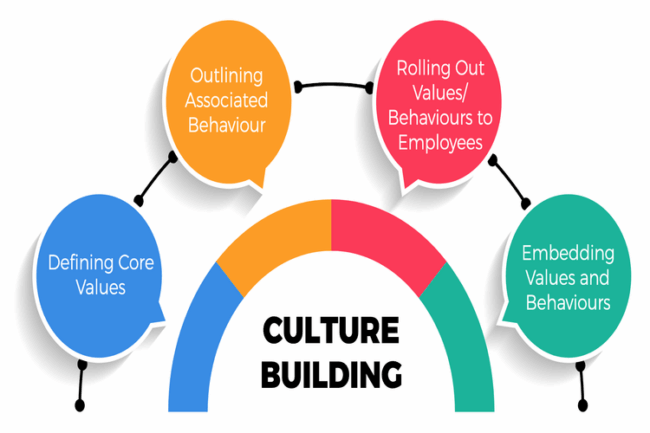
From substation automation to utility-scale wind and solar, our proposals pair Digital Twin + Calculators with Zero-Trust enforcement to secure generation, transmission, and distributed assets while enabling reliable O&M.
|
Engagement Options
| Free Trial |
PoC / fixed
Pilot |
Annual / subscription
Plant/Cluster |
Custom / bundle
Enterprise |
|---|---|---|---|---|
| Passwordless secure remote access | ||||
| Network cloaking (OT invisibility) | ||||
| Software-defined microsegmentation | ||||
| Legacy device shielding (virtual air gap) | ||||
| Vendor & field engineer access | ||||
| Audit & reporting | ||||
| 24/7 Support | ||||
| Start Free | Request Pilot | Get Quote | Talk to Sales |
Measured Outcomes
Advantages
Cloak IP space and restrict access per role; enable telemetry without exposing control networks.
QR+biometric or FIDO2 flows remove passwords and defeat credential theft & MFA fatigue.
Overlay segmentation creates a strong barrier for unpatchable devices and mixed-vendor fleets.
Block reconnaissance & phishing—the first two punches of most attacks—before they reach OT.
Granular policies per plant, feeder, inverter string, or BESS rack to stop lateral movement.
Independent testing shows significant performance gains vs. common alternatives.
Testimonials
Leaders in generation, transmission, and renewables trust Zero-Trust overlays to simplify secure access and reduce risk while keeping operations online.
Head of OT Security Utility Customer
We reduced exposure across remote sites and cut third-party access risk without re-architecting our network.
Renewables O&M Director Wind & Solar
Passwordless SRA and microsegmentation made vendor maintenance safe and auditable.
Grid Engineer Transmission
Cloaking stopped reconnaissance on our edge devices, and policies contained lateral movement attempts.