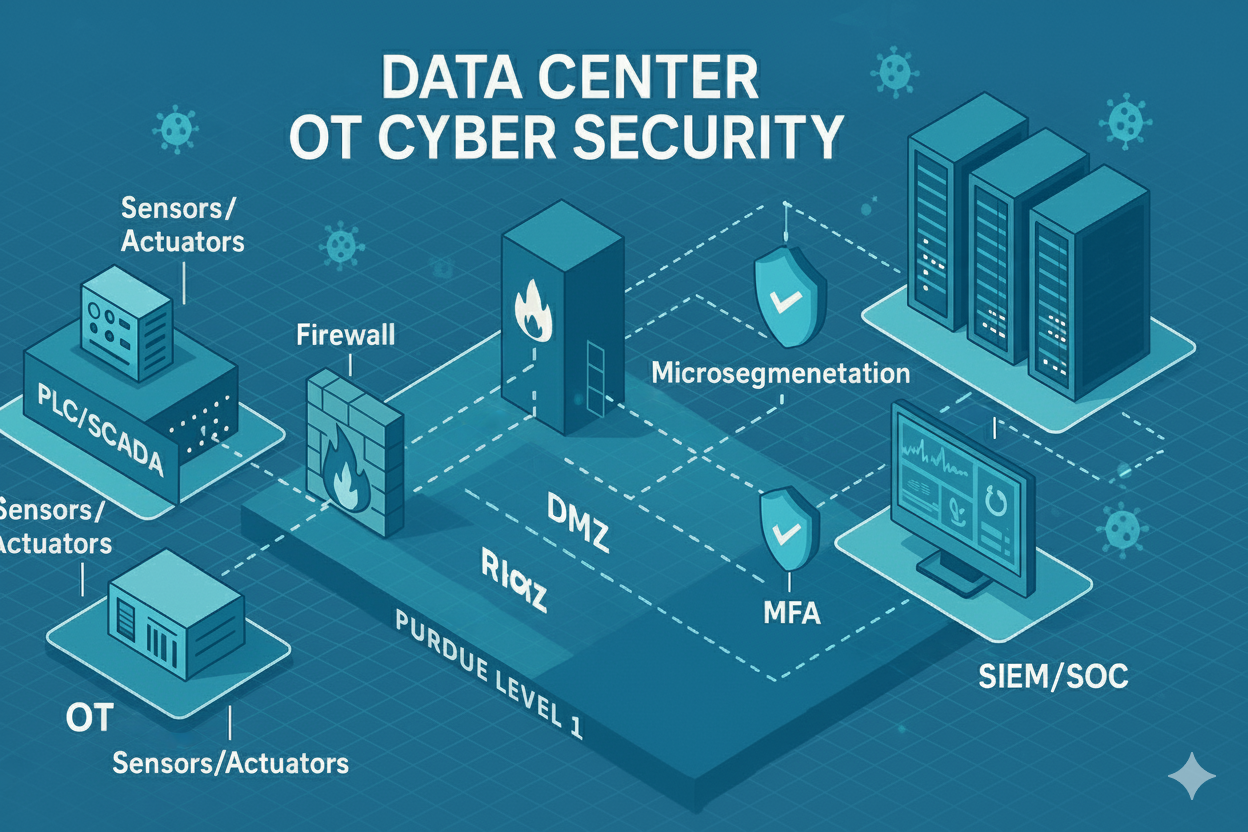
Modern data centers are mission-critical infrastructure. They house power, cooling, environmental controls, physical security, and operational systems required to maintain uptime, integrity, and safety.
With increasing threats such as credential theft, AI-powered reconnaissance, and lateral movement attacks, data center OT networks require robust Zero Trust protection.