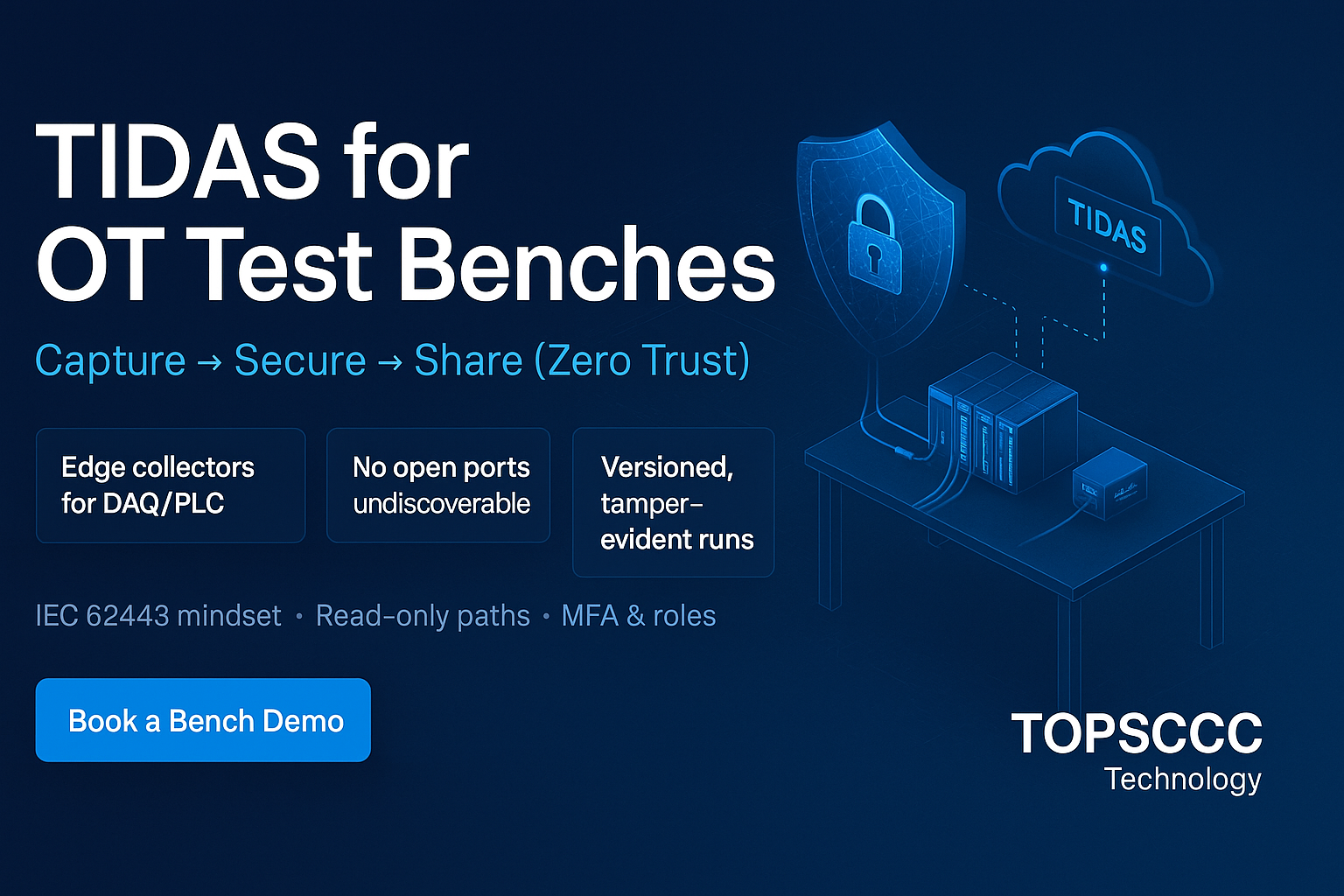
Objective: Reduce attack surface and stop lateral movement across plants, terminals, and data centers by combining device cloaking, network cloaking, and micro‑segmentation with passwordless MFA and zero‑trust orchestration.
How it works:
- Cloak devices and subnets behind an identity‑aware, encrypted SDP overlay—only authenticated identities can even discover endpoints.
- Segment users/hosts/gateways into least‑privilege groups mapped to Purdue levels and business roles.
- Orchestrate via a central controller with SSO/SCIM, policy templates, and one‑click route grants for maintenance windows.
- Modernize with new‑age tech: Cloud deployment, RPA for access workflows, AI/analytics for anomaly insights, Blockchain for immutable access logs, Cloud Computing for elastic scale.