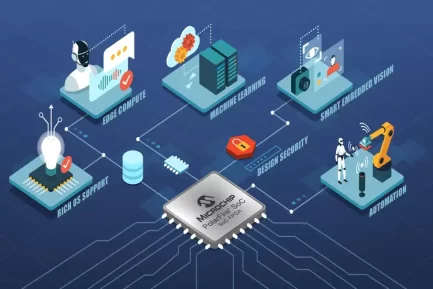
BlastWave-aligned approach
- Make OT invisible: cloak dam SCADA/HMIs, RTUs, PLCs, gateways.
- Verify then connect: passwordless MFA (mobile/FIDO2), device posture, least-privilege.
- Contain failures: microsegment pump houses, spillway gates, hydropower units.
- No IP changes: drop in at the OT DMZ; preserve existing addressing/routes.
Remote maintenance workflow (operators & vendors)
- User opens BlastShield Desktop Client & chooses Mobile App or FIDO2 authentication.
- Scan QR on mobile; biometric confirms identity; ephemeral credentials minted.
- Policy grants access only to approved assets (e.g., Gate-PLC/HMI) for a limited window.
- Launch Orchestrator for session visibility, policy objects, and audit trails.
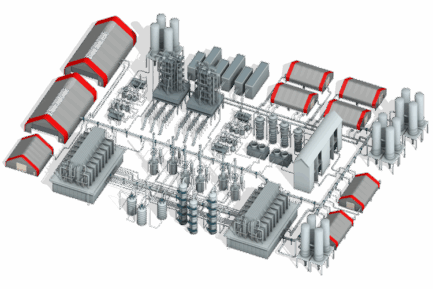
Operations & compliance
- Session logging for regulator audits; vendor access is time-bound & device-scoped.
- Legacy device protection—wrap unpatchable PLCs without inline changes.
- Supports hybrid topologies (reservoirs, pumping stations, control rooms, SOC/NOC).