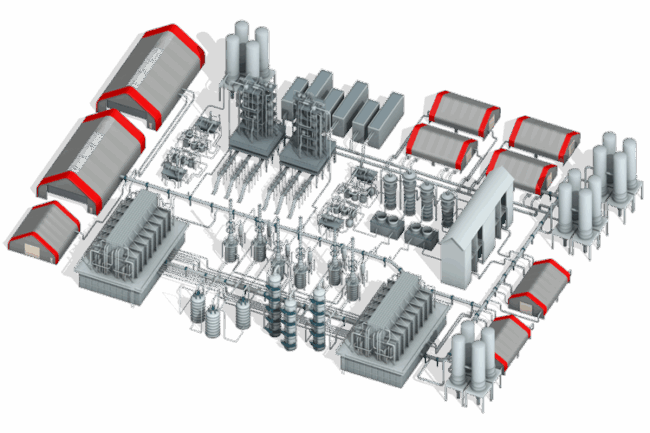
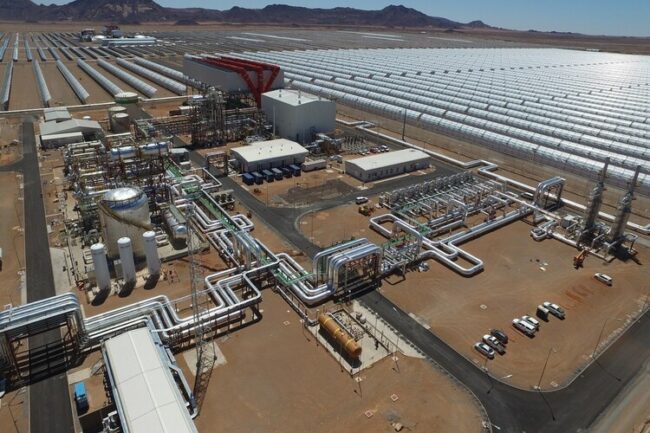
We secure quay and yard cranes, TOS, CCTV, access control, weighbridges, gates and berth automation with an OT-first Zero Trust architecture. Key outcomes:
- admin@topsccc.tech
- Mohan Nagar, Baner, Pune
Ports & Shores Networks
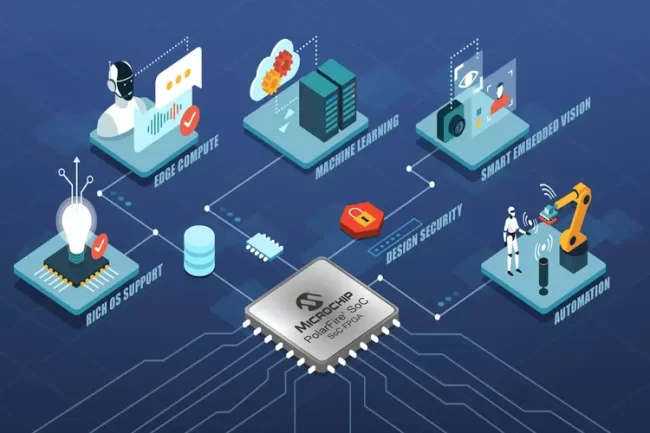
Hide crane controls, TOS, CCTV and access control endpoints from reconnaissance. Cloaking eliminates discovery so attackers can’t even scan your OT assets in port yards, berths, and container terminals.
No usernames, no passwords—FIDO2 keys or mobile authenticator only. Contractors and pilots get least-privilege access without credential theft risk.
Direct, encrypted access to specific PLCs/RTUs/edge gateways—no open inbound ports, no VPN sprawl. Ideal for crane OEMs, AGV and conveyor maintenance.
Create micro-zones for quay cranes, yard cranes, TOS, access control, and surveillance. Stop lateral movement inside flat L2 networks.
Protect unpatchable devices with a software-defined barrier—enforce allowed sessions only; everything else is dropped.
Grant time-boxed, asset-scoped access to OEMs (cranes, gates, weighbridges) with approvals and audit trails.
Gateways run on x86, VMware/Hyper-V, AWS or BlastWave-certified OnLogic—drop-in without re-architecting the port network.
|
Engagement Plans
Ports & Shores OT Security
|
Free
One-time Assessment |
%% / custom
Pilot - 30 Days |
POA / annual
Subscription - Port Wide |
POA / framework
Enterprise - Multi-Port |
|---|---|---|---|---|
| Scope | ||||
| Approach | ||||
| Outcomes | ||||
| Deliverables | ||||
| Support | ||||
| Start Free Trial | Book Pilot | Request Proposal | Talk to CDO |
Ports & Shores: Zero-Trust Built for Operations
| Risk in Ports & Shores | What We Do | Operational Benefit |
|---|---|---|
| AI-powered recon & bot scanning of OT | Network Cloaking hides IPs/ports & drops unsigned traffic | Attack surface minimized; fewer alarms |
| Phishing & credential theft (vendors) | Passwordless MFA (FIDO2 / mobile) | Compromised creds eliminated |
| Flat L2 networks & lateral movement | Software-defined microsegmentation by asset function | Breaches contained to micro-zones |
| Legacy, unpatchable devices | Virtual air-gap gateways (active/passive) | Keep critical ops online, safely |
| Remote maintenance exposure | Peer-to-peer ZTNA with least-privilege policies | Faster MTTR, controlled access |
- Policy-as-Code orchestration with full audit logs
- No inbound open ports; direct encrypted sessions only
- Drop-in gateways for x86/VMware/Hyper-V/AWS/OnLogic
- Rapid pilot on crane block + TOS without re-wiring